htb editor
OS:Linux
Easy
Foothold:
CVE-2025-24893 XWiki 15.10.8
PrivEsc:
CVE-2024-32019 ndsudoRecon
┌──(kali㉿kali)-[~/Work/Work]
└─$ sudo nmap --open 10.10.11.80 -A
[sudo] password for kali:
Starting Nmap 7.95 ( https://nmap.org ) at 2025-11-28 02:36 EST
Nmap scan report for 10.10.11.80
Host is up (1.1s latency).
Not shown: 997 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 3e:ea:45:4b:c5:d1:6d:6f:e2:d4:d1:3b:0a:3d:a9:4f (ECDSA)
|_ 256 64:cc:75:de:4a:e6:a5:b4:73:eb:3f:1b:cf:b4:e3:94 (ED25519)
80/tcp open http nginx 1.18.0 (Ubuntu)
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_http-title: Did not follow redirect to http://editor.htb/
8080/tcp open http Jetty 10.0.20
| http-cookie-flags:
| /:
| JSESSIONID:
|_ httponly flag not set
| http-title: XWiki - Main - Intro
|_Requested resource was http://10.10.11.80:8080/xwiki/bin/view/Main/
|_http-server-header: Jetty(10.0.20)
| http-robots.txt: 50 disallowed entries (15 shown)
| /xwiki/bin/viewattachrev/ /xwiki/bin/viewrev/
| /xwiki/bin/pdf/ /xwiki/bin/edit/ /xwiki/bin/create/
| /xwiki/bin/inline/ /xwiki/bin/preview/ /xwiki/bin/save/
| /xwiki/bin/saveandcontinue/ /xwiki/bin/rollback/ /xwiki/bin/deleteversions/
| /xwiki/bin/cancel/ /xwiki/bin/delete/ /xwiki/bin/deletespace/
|_/xwiki/bin/undelete/
|_http-open-proxy: Proxy might be redirecting requests
| http-methods:
|_ Potentially risky methods: PROPFIND LOCK UNLOCK
| http-webdav-scan:
| WebDAV type: Unknown
| Server Type: Jetty(10.0.20)
|_ Allowed Methods: OPTIONS, GET, HEAD, PROPFIND, LOCK, UNLOCK
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.19
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 8080/tcp)
HOP RTT ADDRESS
1 739.30 ms 10.10.16.1
2 371.46 ms 10.10.11.80
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 60.88 secondsWeb
8080
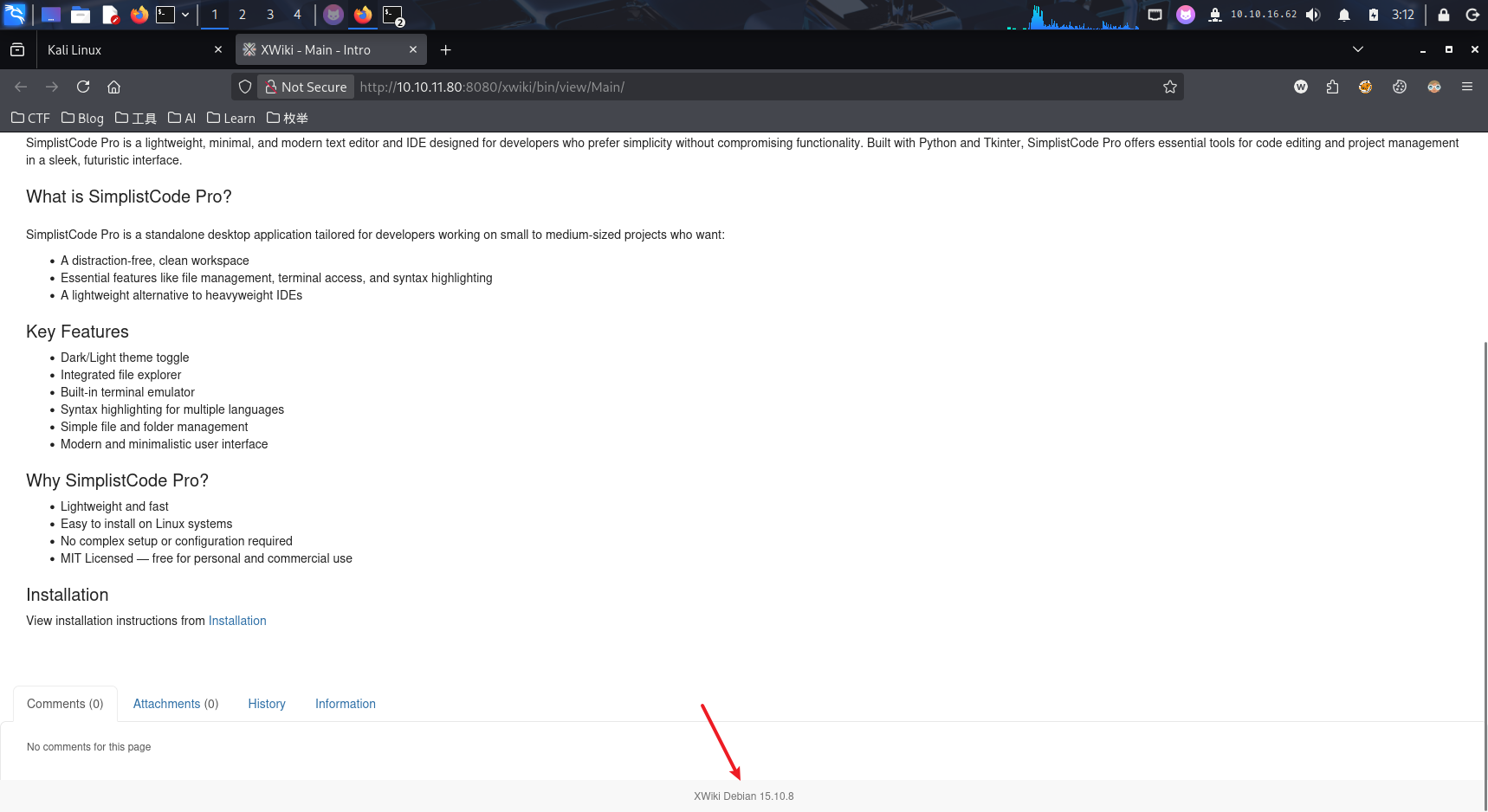
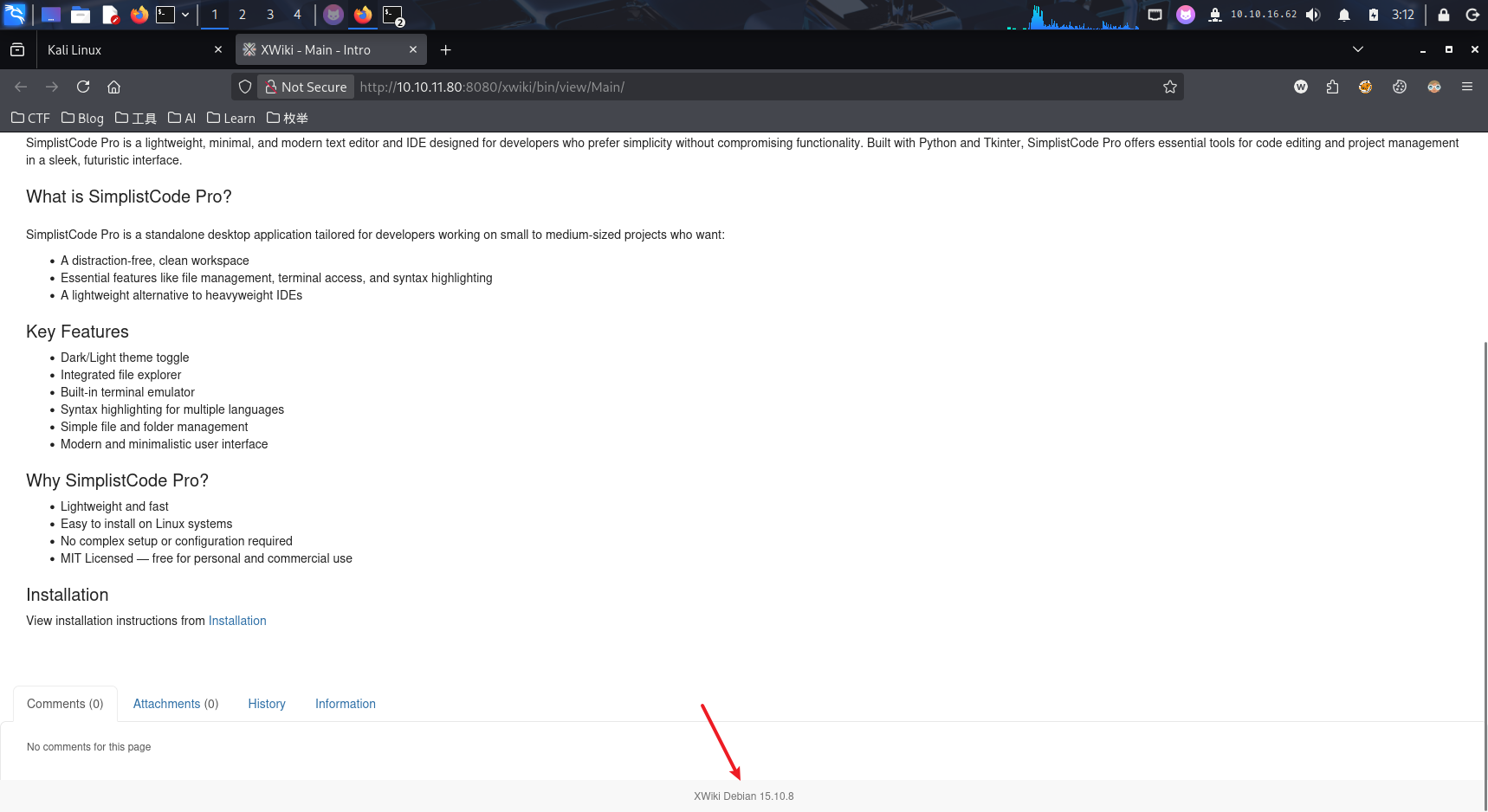
发现版本号XWiki 15.10.8
查看发现此Poc
Foothold
使用后即可得到初步shell
枚举路径后发现
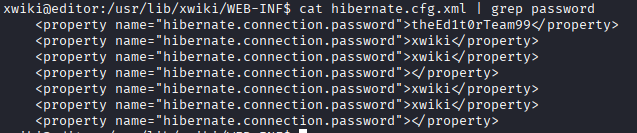
查看/home得到凭据:oliver:theEd1t0rTeam99
PrivEsc
运行linpeas.sh
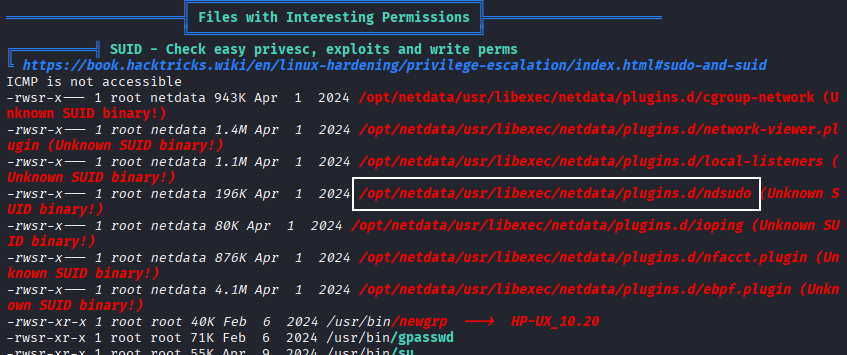
搜索后发现
htb Editor
OS: Linux
Difficulty: Easy
Vulnerabilities Exploited:
- CVE-2025-24893 (XWiki 15.10.8)
- CVE-2024-32019 (ndsudo)
Approach: The exploit takes advantage of the following vulnerabilities to gain elevated privileges:
- CVE-2025-24893: A vulnerability in XWiki’s permission handling allows an attacker to execute arbitrary code with administrative privileges.
- CVE-2024-32019: A vulnerability in the ndsudo tool enables an attacker to execute sudo commands with elevated privileges.
Prerequisites:
- Access to the affected XWiki instance.
- Knowledge of the vulnerabilities and their exploitation techniques.
Steps to Exploit:
- Identify the vulnerable versions of XWiki and ndsudo.
- Exploit CVE-2025-24893 by manipulating XWiki’s permission settings to grant the attacker administrative privileges.
- Use CVE-2024-32019 to execute sudo commands with elevated privileges.
Notes:
- This exploit requires manual intervention and knowledge of the target system’s configuration.
- It is recommended to patch the vulnerabilities as soon as possible to prevent further attacks.
Reconnaissance
┌──(kali㉿kali)-[~/Work/Work]
└─$ sudo nmap --open 10.10.11.80 -A
[sudo] Password for kali:
Starting Nmap 7.95 (https://nmap.org) at 2025-11-28 02:36 EST
Nmap scan report for 10.10.11.80
Host is up (1.1s latency).
Not shown: 997 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 3e:ea:45:4b:c5:d1:6d:6f:e2:d4:d1:3b:0a:3d:a9:4f (ECDSA)
|_ 256 64:cc:75:de:4a:e6:a5:b4:73:eb:3f:1b:cf:b4:e3:94 (ED25519)
80/tcp open http nginx 1.18.0 (Ubuntu)
|_http-server-header: nginx/1.18.0 (Ubuntu)
|_http-title: Did not follow redirect to http://editor.htb/
8080/tcp open http Jetty 10.0.20
| http-cookie-flags:
| /:
| JSESSIONID:
|_ httponly flag not set
| http-title: XWiki - Main - Intro
|_Requested resource was http://10.10.11.80:8080/xwiki/bin/view/Main/
|_http-server-header: Jetty(10.0.20)
| http-robots.txt: 50 disallowed entries (15 shown)
| /xwiki/bin/viewattachrev/ /xwiki/bin/viewrev/
| /xwiki/bin/pdf/ /xwiki/bin/edit/ /xwiki/bin/create/
| /xwiki/bin/inline/ /xwiki/bin/preview/ /xwiki/bin/save/
| /xwiki/bin/saveandcontinue/ /xwiki/bin/rollback/ /xwiki/bin/deleteversions/
| /xwiki/bin/cancel/ /xwiki/bin/delete/ /xwiki/bin/deletespace/
|_/xwiki/bin/undelete/
|_http-open-proxy: Proxy might be redirecting requests
| http-methods:
|_ Potentially risky methods: PROPFIND LOCK UNLOCK
| http-webdav-scan:
| WebDAV type: Unknown
| Server Type: Jetty(10.0.20)
|_ Allowed Methods: OPTIONS, GET, HEAD, PROPFIND, LOCK, UNLOCK
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.19
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 8080/tcp)
HOP RTT ADDRESS
1 739.30 ms 10.10.16.1
2 371.46 ms 10.10.11.80OS and service detection has been completed. Please report any incorrect results at https://nmap.org/submit/.
Nmap results: 1 IP address (1 host up) was scanned in 60.88 seconds.
Web
Port: 8080
Version detected: XWiki 15.10.8
View the POC (Proof of Concept) for this vulnerability:
[https://github.com/dollarboysushil/CVE-2025-24893-XWiki-Unauthenticated-RCE-Exploit-POC/blob/main/CVE-2025-24893-dbs.py]
Initial Access
After gaining initial access, a shell can be obtained. By enumerating paths, the following information was discovered:
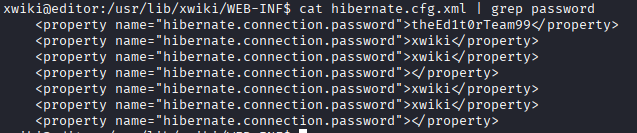 The credentials
The credentials oliver:theEd1t0rTeam99 were found in the /home directory.
Privilege Escalation
The linpeas.sh script was executed to further escalate privileges.
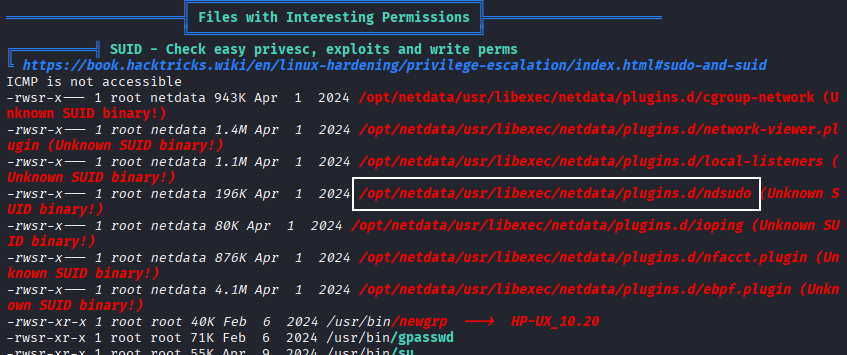 Further investigation revealed the following resource:
https://github.com/dollarboysushil/CVE-2024-32019-Netdata-ndsudo-PATH-Vulnerability-Privilege-Escalation
Further investigation revealed the following resource:
https://github.com/dollarboysushil/CVE-2024-32019-Netdata-ndsudo-PATH-Vulnerability-Privilege-Escalation